در حال بارگذاری...
بدافزار از نگاه مهاجم
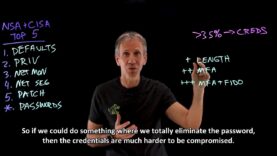
در این ویدیو میخواهیم از دید یک عامل مخرب یا مهاجم به حملهی سایبری نگاه کنیم و ببینیم که این فرد چگونه از بدافزار استفاده کرده و آن را توزیع میکند.
بستن







![AI in Cybersecurity_720.mp4_snapshot_05.42_[2023.09.14_21.43.06]](https://www.apk.co.ir/video/wp-content/uploads/sites/20/2023/09/AI-in-Cybersecurity_720.mp4_snapshot_05.42_2023.09.14_21.43.06-100x75.jpg)